Load Balancer¶
Overview¶
Application Load Balancer (ALB) is a network service that distributes incoming public web traffic between virtual servers to provide fault tolerance for websites and applications.
The Load Balancer (ALB) allows to easily configure web or TLS traffic to virtual machines, belonging to the same Compute service based on a domain name in the HTTP protocol or the Server Name Indication (SNI) extension of TLS.
When the volume of incoming traffic changes dramatically, the balancer evenly distributes the entire volume of requests between resources according to the Round-robin algorithm.
ALB provides automatic renewal of LetsEncrypt certificates and the ability to upload your own certificates. Forwarding through ALB does not require opening virtual machine destination ports in the Network Security Group in the Firewall tab. ALB provides access on the main public address of the account only on ports 80 and 443. These ports can be reassigned in the Port-Forwarding application.
The Health Check feature allows to exclude unhealthy servers from the load balancing rotation. ALB monitors the status of the virtual machines responsible for handling the web traffic route, and will consider VMs healthy as long as they return status codes between 2XX and 3XX to the health check requests (carried out every interval). If a VM is found to be unavailable (powered off or broken), the HealthCheck ensures that web traffic is not directed to that particular VM.
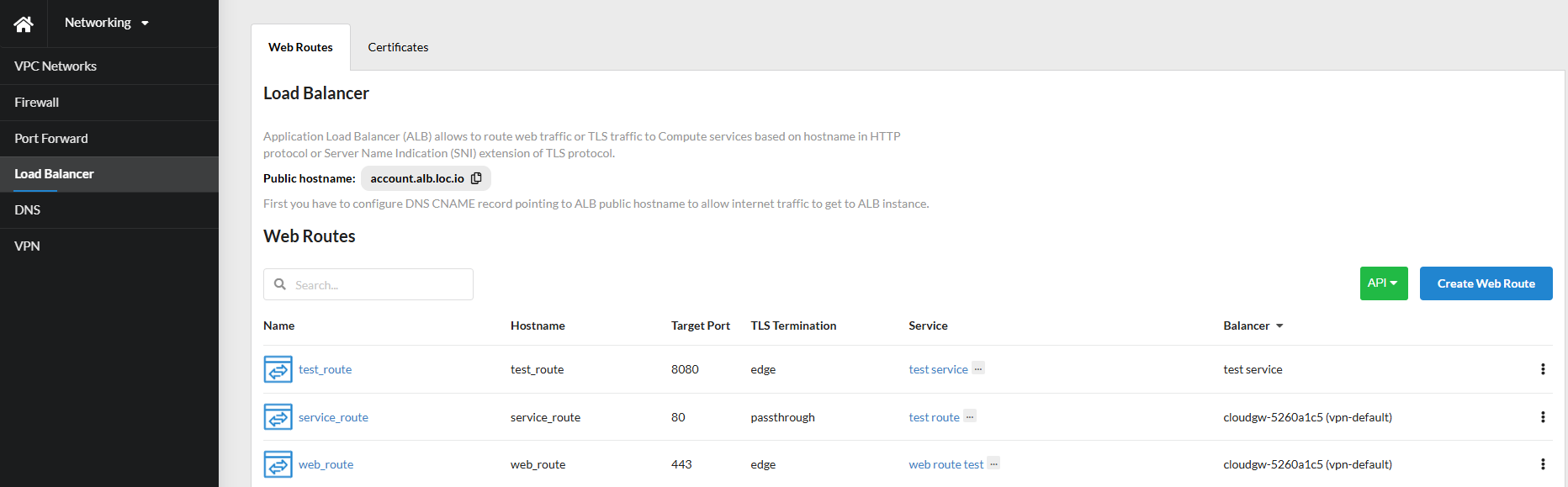
The Web Routes tab contains a list of ALB web traffic routes. The user can create, edit, and delete routes.
Creating and Configuring a Route¶
Preparation¶
Before creating a new route, the user must to configure a DNS CNAME record pointing to the public hostname of the ALB, to allow internet traffic to access the virtual machine through the ALB. Then, the user should prepare the virtual machine.
For information
By default we mean a prepared virtual machine with a web server on port 80.
Route creation¶
- On the
Web Routestab, clickCreate Route. -
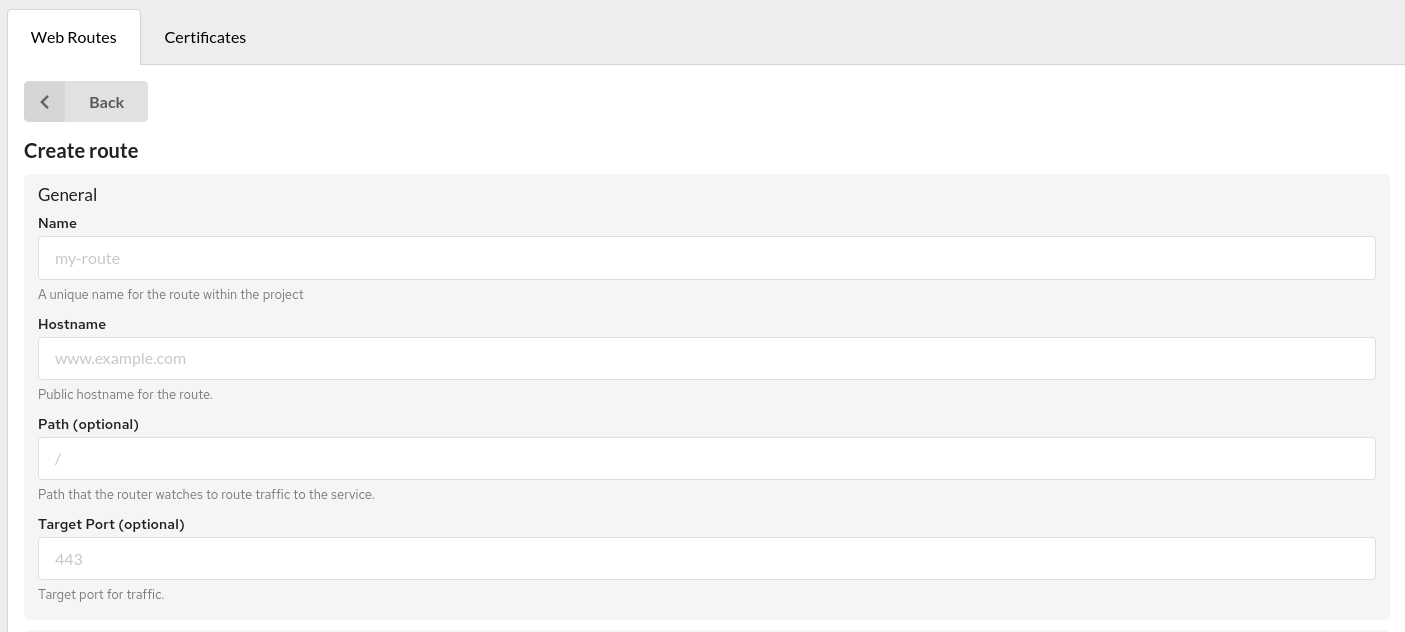
In the popped-up modal window, enter:
Namefor the route within the project;Hostname- public host name for the route;Pathallows matching requests based on the URL path value (optional);Target port- the destination port for traffic (optional);Balancer- Load Balancer instance that serves this route.
-
In the
Target Services, select theService(s)for load balancing (each service has a weight that determines the amount of traffic received). - Select
IP interface type: IPv4/IPv6. -
It is possible to enable route
HealthCheck.
The system automatically checks the status of virtual machines associated with the route. If at least one of them is running, traffic is directed to the available machines.
To configure a route HealthCheck, enter:Path– server URL path for the healthcheck endpoint (optional);Scheme– the URL scheme (http/https) of the server for the healthcheck endpoint (optional);Hostnamein theHostheader of the healthcheck request (optional);Port– the server's URL port for the healthcheck endpoint (optional);Interval– the frequency of healthcheck requests;Timeout– the duration ALB will wait for a health check response before marking the server as unhealthy;- Custom
Headersto be sent to the health check endpoint (optional); Follow Redirectsdefines whether redirects should be followed during healthcheck calls.
-
Select
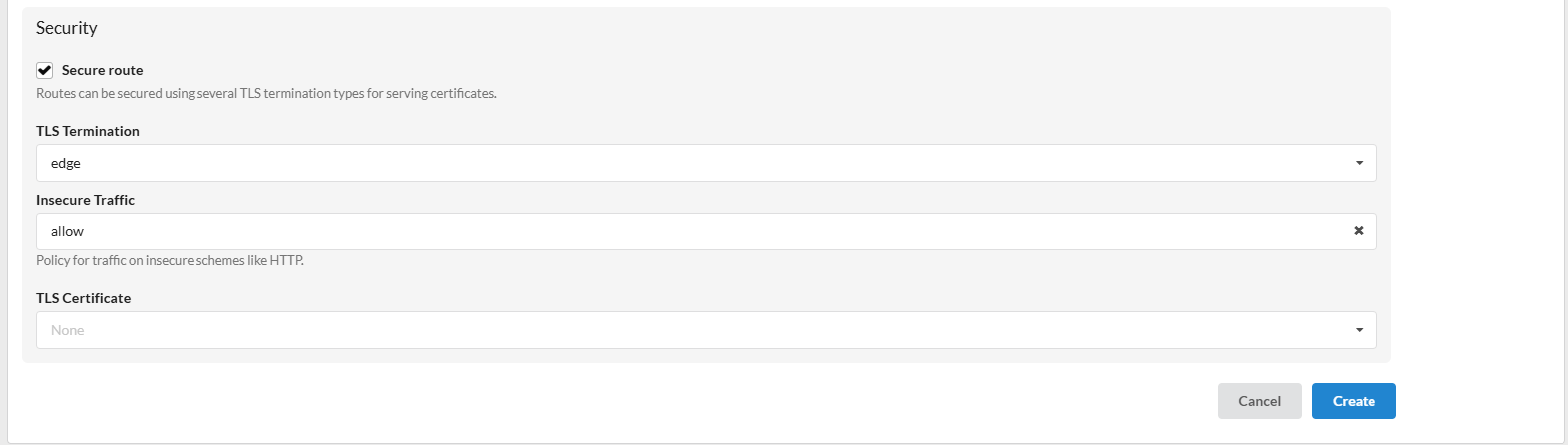
Securitysettings for the routes by enabling theSecure Routecheckbox, or you can leave it disabled.If
Secure Routeis enabled, specify theTLS termination type:- Edge
With edge termination, the encryptedTLS trafficis terminated on the ALB, then the already decrypted traffic is proxied to the internal IP addresses of the virtual machines on theHTTP port (80/TCP). To terminate TLS traffic, the downloaded certificate is used if it matches the Hostname field of the Web route, otherwise, an attempt is made to issue a LetsEncrypt certificate. If the issue of the LetsEncrypt certificate fails for any reason (for example, the DNS record is not set to the ALB public hostname, the request limit has expired), then the default self-signed certificate will be used. - Passthrough
With passthrough termination, encrypted traffic is sent directly to the destination without decrypting the traffic. In this case, the balancer only allocates traffic between services according to weights. This is currently the only method that supports client certificate authentication (also known as two-way authentication). - Re-encrypt
This is a case of edge termination where the TLS protocol is terminated at the ALB with a certificate and then re-encrypts its connection to an endpoint on theHTTPS port (443/TCP), which may have a different certificate. Therefore, the full connection path is encrypted even on the internal network. ALB uses performance checks to determine host availability.
For information
Re-encrypt ALB does not currently validate the destination host certificate, so self-signed certificates can be used.
- Edge
-
Select a policy for traffic on insecure schemes:
- Allow - allows HTTP traffic to pass through;
- Redirect - automatically redirects the client from HTTP to HTTPS (using HTTP code 301).
- None (empty value) – HTTP traffic is completely blocked. The route is available only via HTTPS, and any requests over the insecure protocol will be rejected.
-
Select one of the
TLS Certificatesassociated with this route. - Click
Create.
The new route will appear in the general list, where you can edit its settings or delete it using the side menu or by clicking the corresponding buttons in the Details.
To view the details of the created route, simply click on it.
Security Settings and Routing Types¶
| Secure route | TLS Termination | Insecure Traffic | Route |
|---|---|---|---|
| ✖ | N/A | N/A | HTTP |
| ✔ | Edge | None | HTTPS |
| ✔ | Edge | Allow | HTTPS / HTTP |
| ✔ | Edge | Redirect | HTTPS / HTTP |
| ✔ | Re-encrypt | None | HTTPS |
| ✔ | Re-encrypt | Allow | HTTPS / HTTP |
| ✔ | Re-encrypt | Redirect | HTTPS / HTTP |
| ✔ | Passthrough | None | HTTPS |
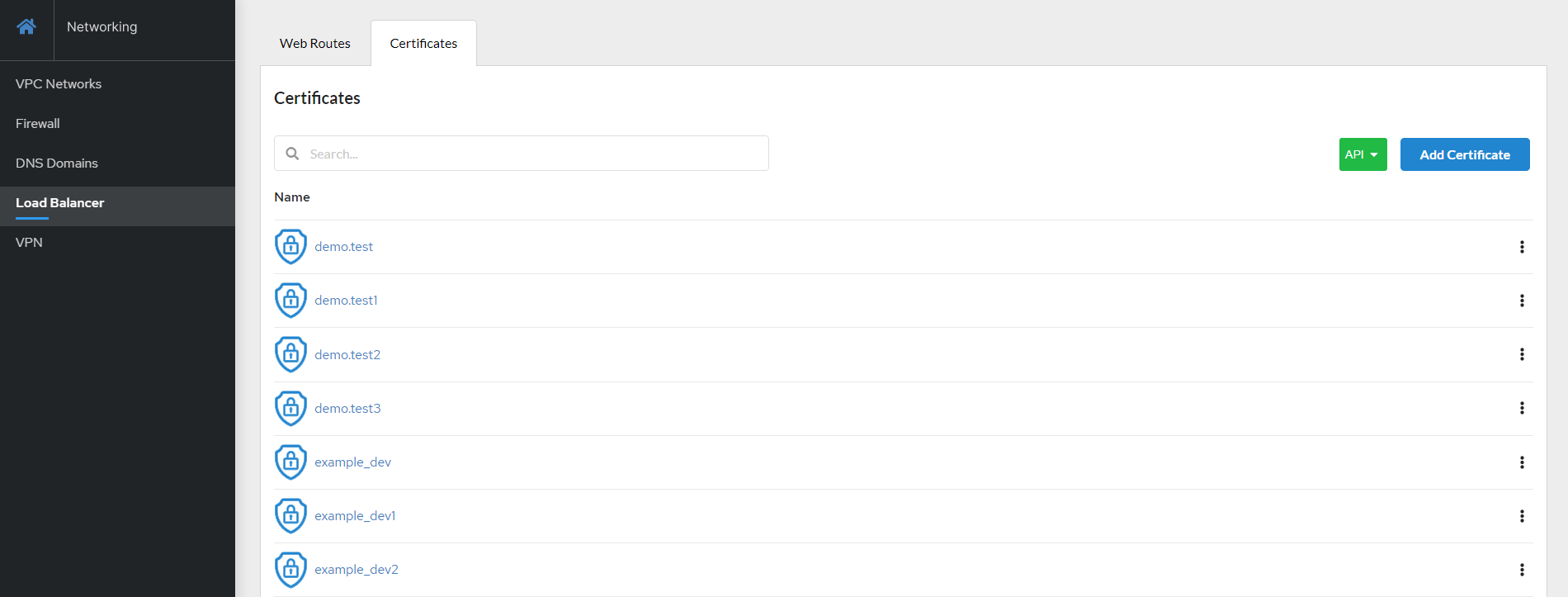
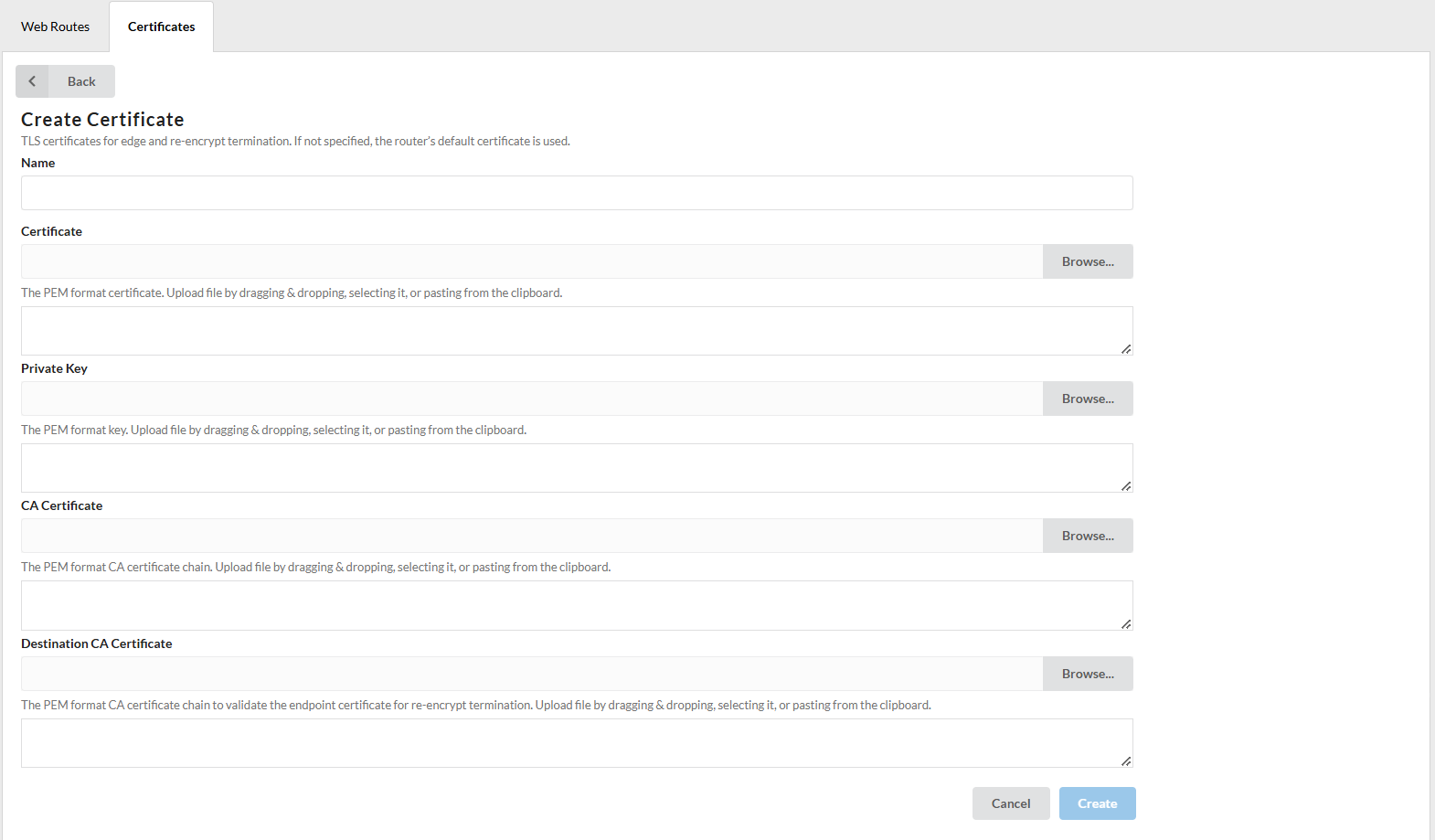
Certificates¶
Users can add TLS certificates for edge and re-encrypted termination on the Certificates tab. Certificates must be in PEM format. Users can add, edit, view, and delete certificates.
Adding Certificates¶
Users can upload certificates by dragging, selecting, or pasting them from the clipboard.
- Click
Addcertificate on theCertificatestab; - Enter a
Namefor the certificates; - Click
Browseand add the needed certificates (or drag and drop, paste from clipboard); - Click
Addto complete.
The certificate will appear on the list. Click on the added certificate to view details.
Users can edit and delete certificates in two ways: using the side menu or by clicking the corresponding buttons in Details.
Own certificates
When using your own certificates, only one certificate related to the domain name must be loaded into the system for correct operation. For example, if the downloaded certificate has expired, you need to delete it and download the current one.
Headers¶
ALB adds and modifies some headers, which are forwarded to the target server.
| Header | Example | Purpose |
|---|---|---|
X-Real-IP |
109.243.1.221 |
Client's real IP address |
X-Forwarded-For |
109.243.1.221 |
Client IP address or list of proxies before ALB |
X-Forwarded-Host |
test.acc1.at.loc.icdc.io |
Web-route hostname |
X-Forwarded-Port |
443 |
Web-route port |
X-Forwarded-Proto |
https |
Web-route protocol |
X-Forwarded-Server |
e60d898781f3 |
ALB internal name |
Roles and permissions¶
| Action | Member | Admin | Owner | Operator |
|---|---|---|---|---|
| Web Routes | ||||
| View Web Route | ✔ only own | ✔ | ✔ | ✔ |
| Create Web Route | ✔ | ✔ | ✔ | ✔ |
| Edit Web Route | ✔ only own | ✔ | ✔ | ✔ |
| Delete Web Route | ✔ only own | ✔ | ✔ | ✔ |
| Certificates | ||||
| View Certificates | ✔ only own | ✔ | ✔ | ✔ |
| Create Certificates | ✔ | ✔ | ✔ | ✔ |
| Edit Certificates | ✔ only own | ✔ | ✔ | ✔ |
| Delete Certificates | ✔ only own | ✔ | ✔ | ✔ |